Computer Systems COMP SCI 2000, 7081 Primary Examination, Semester 1, 2017
Hello, dear friend, you can consult us at any time if you have any questions, add WeChat: daixieit
Primary Examination, Semester 1, 2017
Computer Systems
COMP SCI 2000, 7081
Basic Gates and Boolean Logic
Question 1
(a) Consider the expression:
z ![]() y
y
which is true if the boolean values z and y are not equal. The expression is false otherwise. Answer the following two questions:
i. Draw the truth table for the ![]() operator in terms of z andy. [3 marks]
operator in terms of z andy. [3 marks]
ii. Draw an implementaton of the ![]() operator solely in terms of And, Or and Not gates. [6 marks]
operator solely in terms of And, Or and Not gates. [6 marks]
[Total for Question 1: 9 marks]
Boolean Arithmetic and ALU design
Question 2
For the following questions you may find the information in Figure 2 useful.
(a) Look at the Hack ALU truth-table shown in Figure 2 in the Appendix. Note that it is possible to design the functionality of the ALU a few operations at a time. For this question, we will consider the last line of the table, which describes the Or operation. Answer the following:
i. In the ALU, the Or operation is implemented using an And chip and some other chips and wires. Give the logical expression for the Or operation implemented by the ALU. Your answer must include an And operation. [4 marks]
ii. Using a truth table, show that the expression you gave in part i above is equivalent to the Or operation. [3 marks]
iii. Draw an implementation of a 16-bit Or chip that uses a 16-bit And chip. [3 marks]
[Total for Question 2: 10 marks]
Sequential Logic
Question 3
(a) Look at the following diagram and text description for a program counter (PC) from figure 3.5 of the textbook:
inc load reset
|
|
Chip name: PC // 16-bit counter
Inputs: in[16], inc, load, reset
Outputs: out[16]
Function: If reset(t-1) then out(t)=0
else if load(t-1) then out(t)=in(t-1)
else if inc(t-1) then out(t)=out(t-1)+1 else out(t)=out(t-1)
Comment: "=" is 16-bit assignment.
"+" is 16-bit arithmetic addition.
Draw an implementation of the PC chip without the reset wire. That is, draw an implementation of the PC that can handle signals from the inc and the load wires but doesn’t provide a reset function.
Note, you do not have to express your solution in terms of primitive gates such as Nand. You can use large scale chips such as Inc16. [10 marks]
[Total for Question 3: 10 marks]
Hack Assembler and Machine Code
Question 4
For the following questions you may find the information in Figures 3, 4, 5, 6 and 7 in the appendix of this paper useful.
(a) Look at the following Hack machine code:
0000000000010000
1111110000010000
0000000000010001
1111000111001000
1111110000010000
0000000000000000
1110001100000001
Answer the following:
i. Using the instruction formats in Figures 3, 4, 5, 6, and 7 as a guide, write down the Hack assember instructions that are equivalent to this code. [7 marks]
ii. Describe what the machine code above does. [3 marks]
[Total for Question 4: 10 marks]
Computer Architecture
Question 5
For the following questions you may find the information in Figures 1, 2, 3, 4, 5, 6, 7 and 8 in the appendix of this paper useful.
(a) Draw an implementation of the logic that implements the JNE (jump not- equal-to) part of the C-instruction. The interface for the JNE is:
j1 j2 j3 zr ng
![]()
|
JNE Logic |
load
where the inputs are the jump wires from the C instruction and the zr and the ng wires from the ALU and the ouput is the load wire for the PC register. Note that you do not have to implement the logic for every type of jump – just JNE. Hint, in answering your question you may find the information in Figure 7 useful. [6 marks]
(b) Consider the following diagram of the Hack CPU.
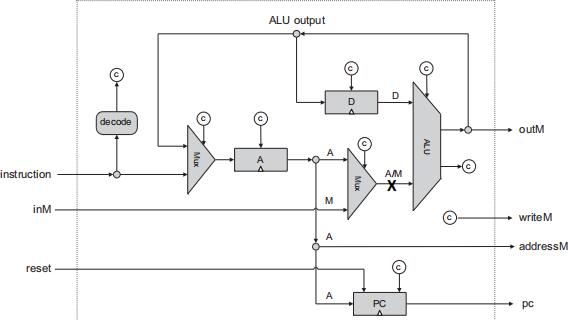
The A/M wire, marked with an X, selects either the A-register or RAM as one of the input values for a C-instruction. In the Hack machine a C-instruction cannot access both the A-register and RAM as input in the same instruction. So, for example, the following instruction:
D=M+A
Is not a valid Hack instruction since it has both M and A as input.
Briefly describe why such access is unlikely to be useful even if it were permit- ted by the Hack machine. [3 marks]
[Total for Question 5: 9 marks]
Assembler
Question 6
(a) Look at the following Hack assembler code:
@x
M=0
@y
M=0
(LOOP)
@x
MD=M+1
@y
M=M+D
@3
D=D-A
@LOOP
D;JLE
Hand-assemble this code by writing out the binary machine code the assembler would produce. For this question you may find the information in Figures 3, 4, 5, 6, and 7 useful. [12 marks]
[Total for Question 6: 12 marks]
Virtual Machine - Expressions
Question 7
(a) Translate the following Jack let statement into Hack Virtual Machine lan- guage:
let d = (2 - x) * (y + 5)
The variables d, x and y are in memory segment local at indexes 2,5 and 7 respectively. Assume there is a function named multiply that will take two arguments and return the result of multiplying the two numbers together. [8 marks]
[Total for Question 7: 8 marks]
Virtual Machine - Subroutines
Question 8
(a) The Hack Virtual Machine language provides three function related commands:
● call f m
● function f n
● return
i. Briefly describe the arguments to the function command. [3 marks]
ii. If the function command did not have the second argument, what alter-nate virtual machine code would need to be generated to implement: function c. x 2 ? [4 marks]
iii. Why does the second argument to the call command need to be pro- vided? [3 marks]
[Total for Question 8: 10 marks]
Jack
Question 9
(a) How does the Jack compiler provided with the nand2Tetris tools ensure that a constructor, function or method from another class is being called correctly? Why does it do this? [3 marks]
(b) List the syntax errors in the following Jack class definition:
01 class x
02 {
03 function int xx(var int n)
04 {
05 if ( n <= 2 ) return 17 ;
06 return y. xxx(n--) ;
07 }
08 }
[5 marks]
[Total for Question 9: 8 marks]
Parsing
Question 10
(a) Turn the following Jack code fragment into XML with one node for each non- terminal in the grammar.
let x[ix] = y ;
You should start with a node for a let statement and you may omit nodes for any keywords, identifiers or symbols. The grammar can be found in Figure 9 in the appendix. [8 marks]
[Total for Question 10: 8 marks]
Code Generation
Question 11
(a) Consider the following Jack method:
// class Complex contains 4 instance variables
// declared in this order: aa, bb, cc and dd, aa is an Array method Complex useful(Complex a, Complex b)
{
}
What Hack Virtual Machine language code would implement the following Jack pro- gram fragments if they were in the body of the method useful?
i. let b = Complex.new(3,2) ;[4 marks]
ii. aa[7] = a ; [6 marks]
iii. return b ; [2 marks]
iv. let bb = dd ; [3 marks]
(b) Show the two symbol tables for the following code just after the variable declaration in the method getSerial has been parsed.
class SerialNums
{
static int id ;
field int myid ;
constructor SerialsNums new(int key)
{
let myid = id ;
return this ;
}
method int getSerial(int password)
{
var int ignore_me ;
return myid ;
}
}
[4 marks]
[Total for Question 11: 19 marks]
Jack OS, Optimisation
Question 12
(a) Why might implementing a 16-bit multiply operation in the ALU of the Hack machine significantly increase the time it takes to execute an instruction that sets the A and D registers to the value 0? [3 marks]
(b) What three aspects of a processor’s physical implementation determine the power consumption and how is this calculated? [4 marks]
[Total for Question 12: 7 marks]
2023-06-21
